date: jan 29, 2026
topic: cloud automation, anti-fingerprinting, resource arbitration
classification: technical procedure / vulnerability disclosure
oracle cloud's "out of host capacity" error (http 500) for free-tier arm instances (vm.standard.a1.flex) functions as a soft limit based on temporal resource contention rather than a hard account restriction. by implementing high-frequency, authenticated api polling coupled with identity-layer obfuscation (residential proxies and canvas fingerprint spoofing), users can exploit race conditions in the provisioning queue to secure maximum-spec instances (4 ocpus, 24gb ram) that are otherwise unavailable via the web console.
when a user attempts to create an arm instance in a popular region (ashburn, frankfurt, tokyo), the console almost invariably returns 500 internal server error: out of host capacity.
this is not a hard denial. it is a temporal state.
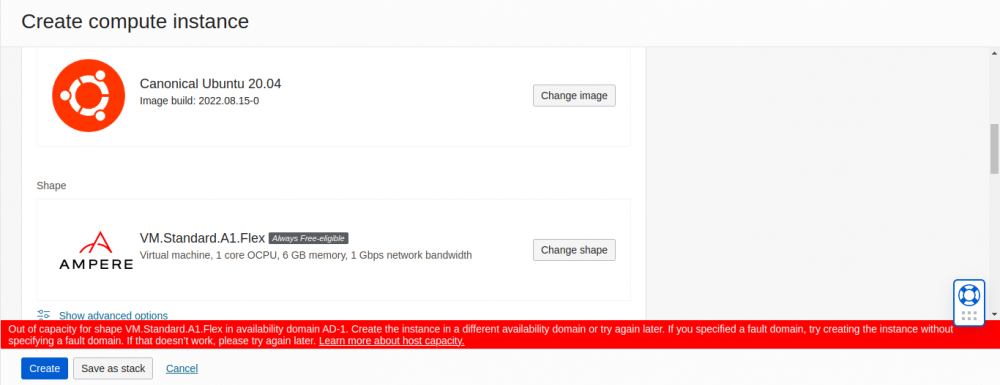 the boss fight: oracle's polite way of saying "go away"
the boss fight: oracle's polite way of saying "go away"
the exploitation technique relies on three distinct phases: identity engineering (to create the account), autonomous sniping (to provision resources), and stealth access (to maintain the account).
before any automation can run, you must possess a valid oci account. this is the hardest step due to oracle adaptive access manager (oaam).
oaam aggregates data to generate a "fraud risk score":
tools required:
steps:
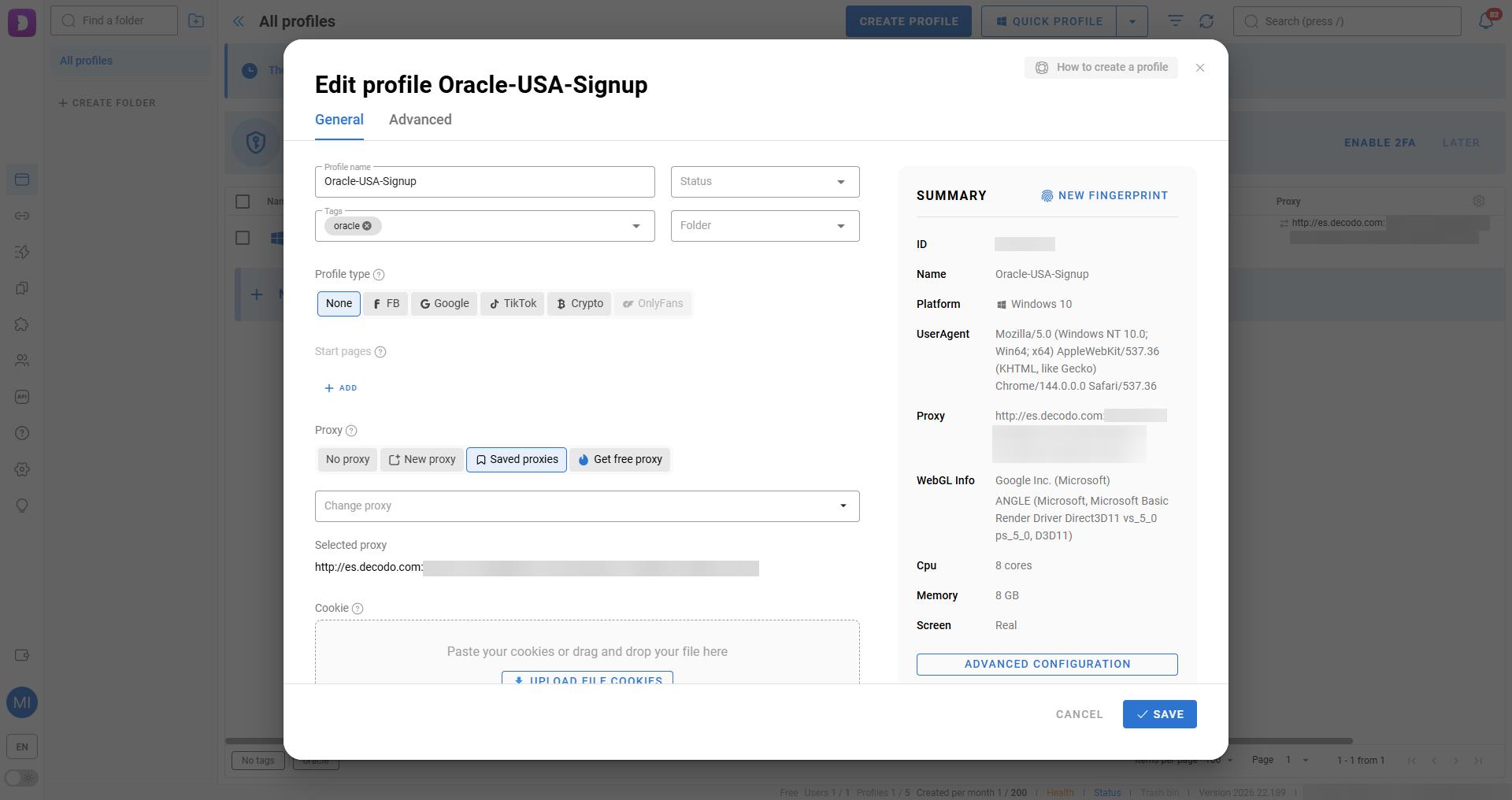 generating a new digital soul in dolphin
generating a new digital soul in dolphin
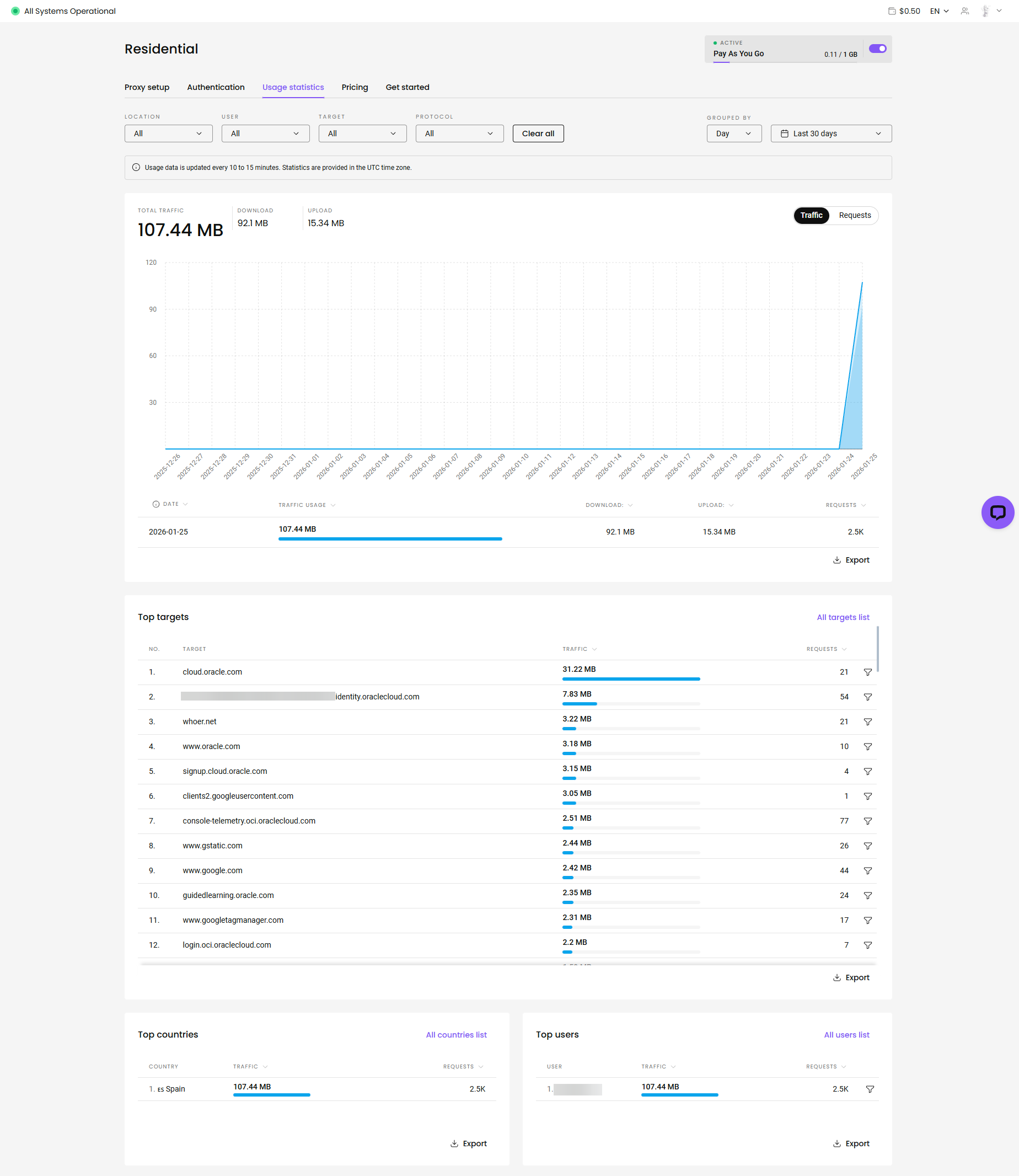 total cost: $4.84 ($4.00 + $0.84 (21% VAT). cheaper than a starbucks latte.
total cost: $4.84 ($4.00 + $0.84 (21% VAT). cheaper than a starbucks latte.
this phase moves the battle from the browser to the api. we deploy a persistent python daemon on a local server (nas/raspberry pi) to handle the race condition.
the attack runs on a low-power linux host.
directory structure:
/home/microck/oracle-sniper/ ├── main.py # the logic core ├── setup_init.sh # process wrapper & monitoring ├── oci.env # secrets configuration ├── oci_config # oci sdk config ├── oci_api_key.pem # your private api key └── requirements.txt # dependencies
oci_config)bypass the gui entirely. generate an api signing key in the oracle console (user settings -> api keys).
file: oci_config
[default] user=ocid1.user.oc1..aaaa... fingerprint=xx:xx:xx... key_file=/home/microck/oracle-sniper/account_ashburn/oci_api_key.pem tenancy=ocid1.tenancy.oc1..aaaa... region=us-ashburn-1
oci.env)this file controls the sniper's targeting parameters.
file: oci.env
# target definition oci_compute_shape=vm.standard.a1.flex # ubuntu 22.04 aarch64 image ocid (region specific!) oci_image_id=ocid1.image.oc1.iad.aaaaaaaa... ocpus=4 memory_in_gbs=24 # network targets # must pre-create a vcn and subnet in the console! oci_subnet_id=ocid1.subnet.oc1.iad.aaaaaaaa... assign_public_ip=true # attack frequency # < 60s risks "toomanyrequests" (429) rate limiting request_wait_time_secs=60 # notification channels discord_webhook=https://discord.com/api/webhooks/...
main.py)the script implements a specific state machine to handle oracle's error codes.
key logic: error handling
oracle returns specific codes when capacity is full. the script must distinguish between "fatal error" (config wrong) and "soft error" (try again).
def handle_errors(command, data, log):
# these are not failures. they are "wait" signals.
soft_errors = [
"toomanyrequests",
"out of host capacity",
"internalerror",
"bad gateway"
]
if data["code"] in soft_errors:
log.info(f"soft limit hit: {data['code']}. sleeping...")
time.sleep(wait_time)
return true # retry allowed
# anything else is a real crash
raise exception(f"fatal error: {data}")
key logic: the launch loop
def launch_instance():
# loop until success
while not instance_exist_flag:
try:
compute_client.launch_instance(...)
# if we get here, we won.
send_discord_message("🎉 sniped!")
break
except serviceerror as e:
# handle the 500/429 errors
handle_errors(...)
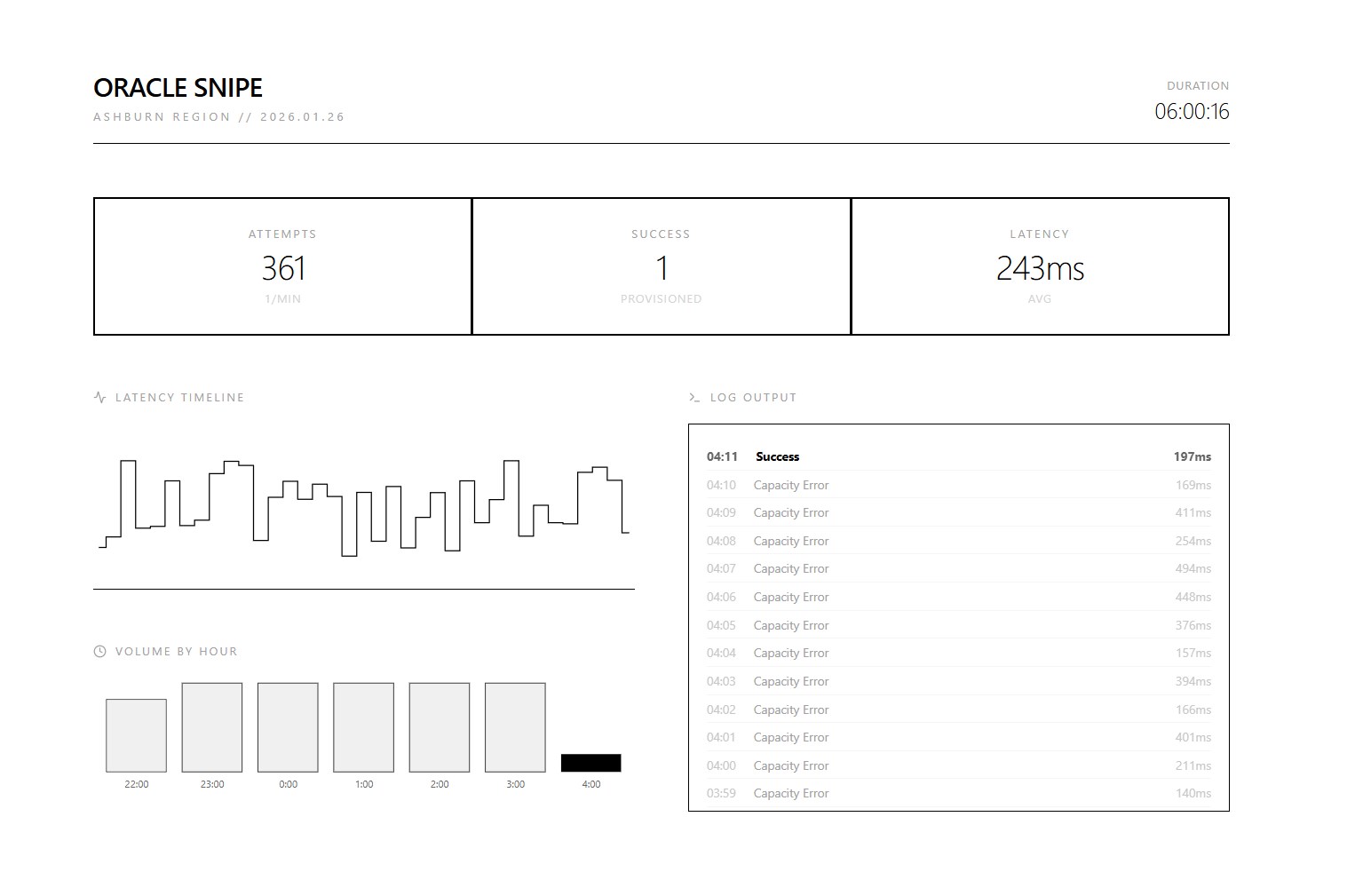 gotcha. the moment the sniper fired.
gotcha. the moment the sniper fired.
we use nohup (no hang up) to ensure the process survives ssh disconnection.
command:
chmod +x setup_init.sh ./setup_init.sh
monitoring logs:
tail -f launch_instance.log
output (normal operation):
2026-01-25 22:11:03 - info - command: launch_instance-- output: {'status': 500, 'code': 'internalerror', 'message': 'out of host capacity.'}
2026-01-25 22:12:04 - info - command: launch_instance-- output: {'status': 500, 'code': 'internalerror', 'message': 'out of host capacity.'}
once the instance creates, accessing it carelessly will get you banned. if your "identity" ip (spain proxy) created the account, but your "access" ip (home ip) logs in via ssh, oracle links the two.
the "clean" link:
do not ssh directly. tunnel traffic through a neutral, trusted intermediary.
scenario:
oracle-paris instance (or any cheap vps).oracle-ashburn instance.ssh config (~/.ssh/config):
# 1. the jump host (the mask)
host oracle-paris
hostname 141.145.xxx.xxx
user ubuntu
identityfile ~/.ssh/id_rsa_paris
# 2. the target (hidden behind paris)
host oracle-ashburn
hostname 10.0.0.x # use private ip if vpn'd, or public ip
user ubuntu
proxyjump oracle-paris # <--- the key
identityfile ~/.ssh/id_rsa_ashburn
traffic flow:
home pc -> (encrypted) -> paris vps -> (encrypted) -> ashburn instance
to oracle's logs in ashburn, the connection comes from the paris ip, not your home ip.
retrieving logs from the nas confirms the methodology works.
file: instance_created
instance id: ocid1.instance.oc1.iad.anuwcljt6jdfblacplxseahalwablmit2csfvgj3gx47n5npd23d5zwnuega display name: ashburn-sniper-instance availability domain: mnay:us-ashburn-ad-1 shape: vm.standard.a1.flex state: provisioning
the script successfully negotiated the race condition, provisioned the resource, and alerted the user via discord.
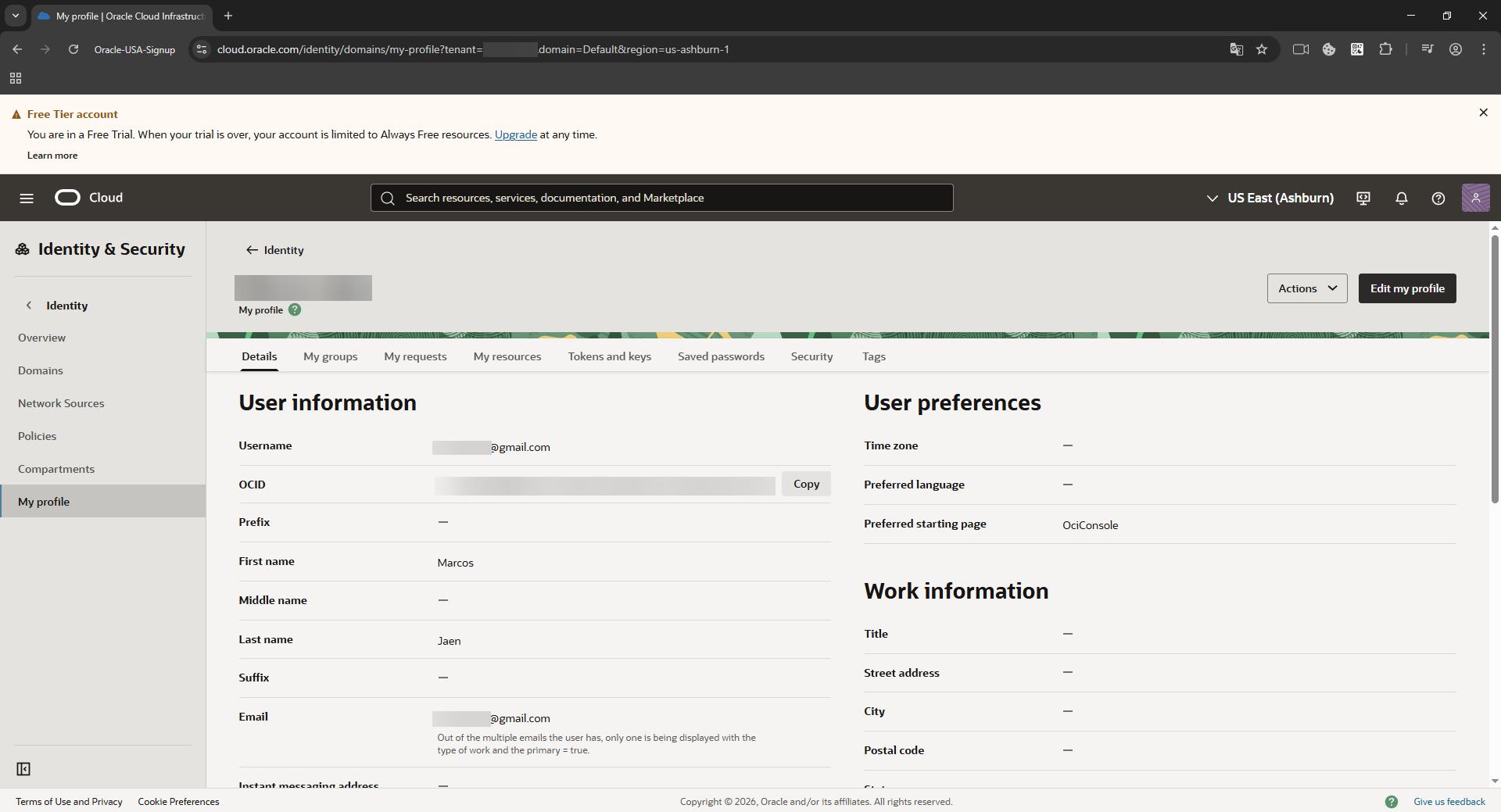 in. account created successfully. the sniper is now active.
in. account created successfully. the sniper is now active.
to mitigate this exhaustion and evasion technique, cloud providers should:
launch_instance api calls on free-tier tenancies. this makes high-frequency polling computationally expensive for the attacker.